The WordPress® REST API is the primary bridge to modern frontend frameworks. However, default endpoints are generic by design. Custom endpoints require precise logic to avoid over-fetching data and exhausting server resources. A poorly architected custom endpoint can become a major performance bottleneck.
Building lean endpoints is essential for respecting the server’s PHP worker pool and memory limits. This ensures your API remains a performance asset rather than a liability. In this article, we examine how to architect high-performance custom endpoints by implementing selective data retrieval, efficient object caching, and network-level security.
How to Architect Lean Responses
One of the most effective ways to optimize an endpoint is to support the native _fields parameter. This allows the client to request only the specific data points it needs. This reduces the size of the JSON payload and the memory required to generate the response.
You should also avoid using standard WP_Query when it is not strictly necessary. WP_Query is a heavy operation that often triggers unnecessary metadata and taxonomy lookups. For surgical data retrieval, using $wpdb directly can significantly reduce memory overhead.
Implementing _fields Support
When registering a custom route, you can implement a filter to prune the response based on the client’s request.
add_action( 'rest_api_init', function () {
register_rest_route( 'my-plugin/v1', '/data/', array(
'methods' => 'GET',
'callback' => 'get_custom_data',
'permission_callback' => '__return_true',
) );
} );
function get_custom_data( $request ) {
$data = array(
'id' => 101,
'name' => 'Performance Plugin',
'version' => '2.1.0',
'author' => 'Delicious Brains',
);
// Check if the _fields parameter is present
if ( isset( $request['_fields'] ) ) {
$fields = wp_parse_list( $request['_fields'] );
$data = array_intersect_key( $data, array_flip( $fields ) );
}
return rest_ensure_response( $data );
}
The Caching Layer: Beyond the Database
You should almost never generate a complex API response on every single request. Using the Transients API allows you to store expensive results in an object cache. This prevents repeated hits to the database and significantly speeds up Time to First Byte (TTFB).
Understanding the Object Cache Layer
In a standard WordPress setup, transients are stored in the wp_options table. This means every time you fetch a transient, WordPress still has to perform a database query. An object cache layer changes this by storing that data in the server’s RAM instead of on the disk.
Keeping frequently accessed data in memory reduces the time it takes to access the database and keeps your server healthier by saving it from searching for the same information repeatedly.
Setting Up Your Own Caching Layer
If your hosting provider does not offer a managed solution, you can implement one yourself. The process generally involves two main components:
- Installing a Persistent Data Store: You will need to install a tool like Redis or Memcached on your server. These are specialized systems designed for high-speed, in-memory data storage.
- Connecting WordPress: Once the store is running, you need an object cache drop-in. This is a specialized PHP file (
object-cache.php) placed in yourwp-contentfolder that tells WordPress to routeset_transientandget_transientcalls to your new data store instead of the database.
Caching with Managed Hosting
Your host may already include solutions for this that require no manual configuration. If you are hosting with WP Engine, the object cache layer is enabled by default on all new environments. It can also be toggled manually within the WP Engine User Portal.
When using this managed layer, you must be mindful of the 1MB buffer size limit. Because the object cache stores data as a single long row, an oversized API response can cause the cache to reject the request. This can lead to a loop of failed requests and 502 Bad Gateway errors. To maintain a healthy environment, aim to keep your cached payloads under 800,000 bytes.
Security: Protecting the Gateway
A custom endpoint is a gateway into your database. It must be built with both a lock and a filter. Every route should include a permission_callback to ensure the requester is authorized to access the data.
You must also use validate_callback and sanitize_callback for every input argument. These functions protect your site against SQL injection and malformed data. For state-changing requests like POST or DELETE, ensure you are properly handling nonces or authentication headers to prevent unauthorized access.
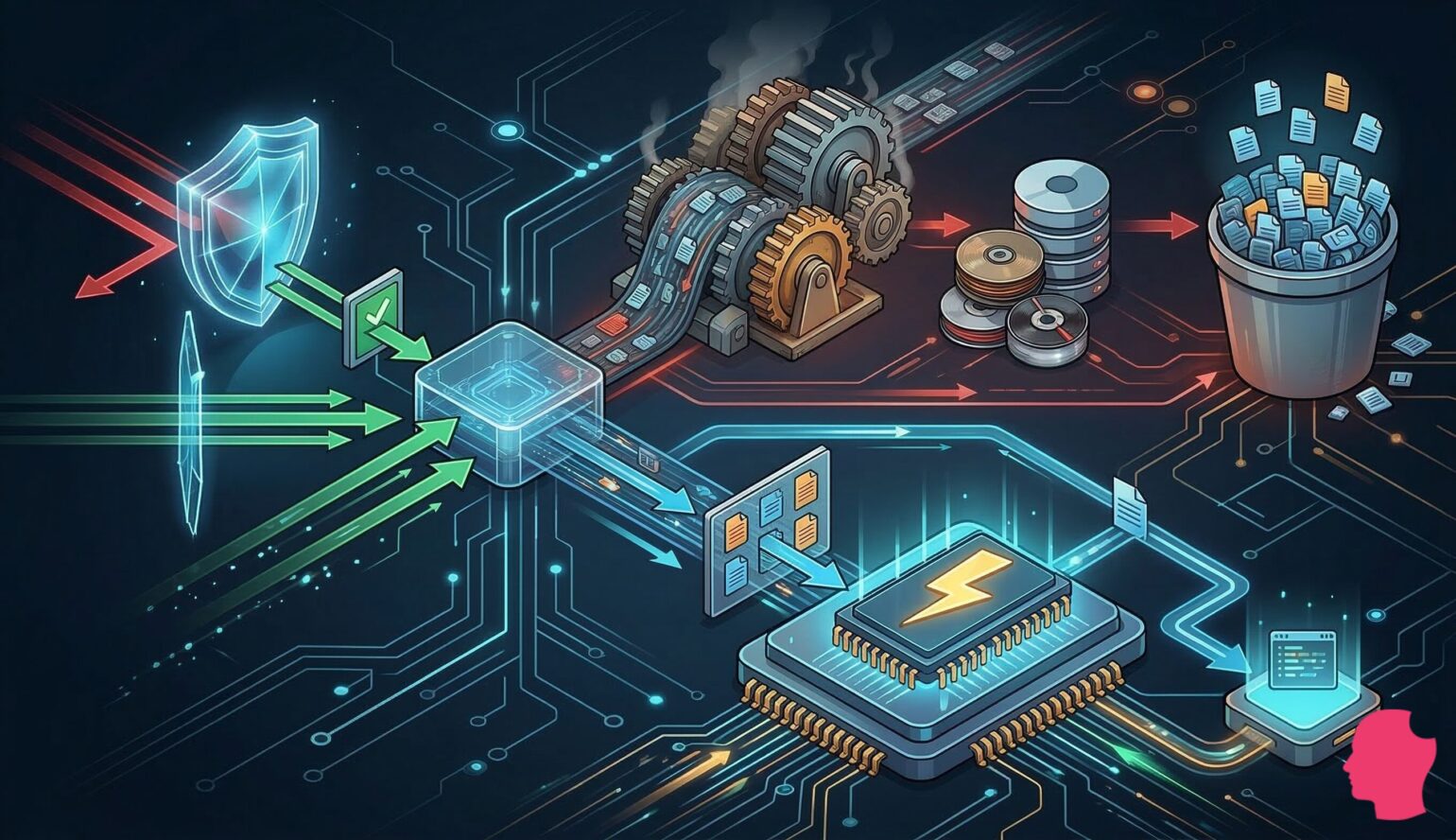
Infrastructure Defense: Rate Limiting and Edge Security
Even a secure endpoint is vulnerable to API hammering. This is a scenario where an external script, bot, or malicious actor targets your custom endpoint with a high volume of requests. Because custom REST API requests are often uncacheable and resource-intensive, they can quickly exhaust your site’s PHP worker pool. This saturation prevents legitimate visitors from accessing the site, effectively resulting in a denial-of-service state.
To protect your server resources, you should look for security solutions that operate at the network edge rather than within WordPress itself.
Why Edge Security Matters
Traditional WordPress security plugins run as part of the application. This means every malicious request still has to be processed by your server before the plugin can block it. In contrast, edge security sits in front of your hosting environment. It acts as a high-performance barrier that filters traffic before it ever touches your WordPress install.
A robust edge strategy includes several key components:
- Web Application Firewall (WAF): A WAF uses a set of rules to identify and block common exploits, such as SQL injection or cross-site scripting, at the network level.
- DDoS Protection: High-capacity networks can absorb and mitigate large-scale distributed denial-of-service attacks that would otherwise overwhelm a single server.
- Network-Level Rate Limiting: By identifying high-frequency requests from specific IP addresses, the edge layer can block API hammering before it reaches your PHP workers.
Strategic Implementations
If you are managing your own infrastructure, you can implement these protections using services like Cloudflare or specialized Nginx configurations. These tools allow you to set strict limits on how often a specific user or bot can hit your /wp-json/ endpoints.
Your host may include these protections as part of their service. For example, WP Engine offers Global Edge Security (GES). This managed solution leverages a global network to provide WAF protection and DDoS mitigation. Server resources are preserved for your actual users while malicious traffic is discarded at the edge.
Conclusion
Responsible API requests consider the health of the entire ecosystem, from the client’s data needs to the server’s available memory. Throughout this guide, we have explored how to move beyond basic endpoint registration toward a more defensive and performant architecture.
By implementing the _fields parameter and avoiding the overhead of standard WP_Query wrappers, you can ensure that your payloads remain lean and fast. We have also seen how the addition of an object cache layer is critical for preventing redundant database queries. Moving frequent lookups into memory reduces the strain on your database and improves response times across the board.
Finally, we discussed why securing the gateway to your database requires more than just code-level sanitization. True infrastructure defense involves shifting the burden of malicious traffic away from your PHP workers and toward the network edge. Combining these code-level optimizations with network-level rate limiting and WAF protection creates a robust system capable of handling high-traffic demands. This comprehensive approach ensures that your WordPress site remains stable, secure, and ready to scale.